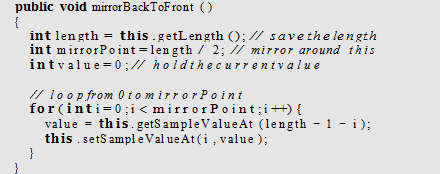
Write a method similar to Program 79 that mirrors from back to front.
What will be an ideal response?
Computer Science & Information Technology
You might also like to view...
Terminal operations are ________; they perform the requested operation when they are called.
a. immediate b. idle c. lazy d. eager
Computer Science & Information Technology
What is the difference between their permissions?
Directory and Permissions a. Change back to the /home/analyst/lab.support.files directory and issue the ls -l command to list all the files with details:
[analyst@secOps second_drive]$ cd ~/lab.support.files/ [analyst@secOps lab.support.files]$ ls -l total 580 -rw-r--r-- 1 analyst analyst 649 Jun 28 18:34 apache_in_epoch.log -rw-r--r-- 1 analyst analyst 126 Jun 28 11:13 applicationX_in_epoch.log drwxr-xr-x 4 analyst analyst 4096 Aug 7 15:29 attack_scripts -rw-r--r-- 1 analyst analyst 102 Jul 20 09:37 confidential.txt -rw-r--r-- 1 analyst analyst 2871 Dec 15 2016 cyops.mn -rw-r--r-- 1 analyst analyst 75 May 24 11:07 elk_services -rw-r--r-- 1 analyst analyst 373 Feb 16 16:04 h2_dropbear.banner -rw-r--r-- 1 analyst analyst 147 Mar 21 15:30 index.html -rw-r--r-- 1 analyst analyst 255 May 2 13:11 letter_to_grandma.txt -rw-r--r-- 1 analyst analyst 24464 Feb 7 2017 logstash-tutorial.log drwxr-xr-x 2 analyst analyst 4096 May 25 13:01 malware -rwxr-xr-x 1 analyst analyst 172 Jul 25 16:27 mininet_services drwxr-xr-x 2 analyst analyst 4096 Feb 14 2017 openssl_lab drwxr-xr-x 2 analyst analyst 4096 Aug 7 15:25 pcaps drwxr-xr-x 7 analyst analyst 4096 Sep 20 2016 pox -rw-r--r-- 1 analyst analyst 473363 Feb 16 15:32 sample.img -rw-r--r-- 1 analyst analyst 65 Feb 16 15:45 sample.img_SHA256.sig drwxr-xr-x 3 analyst analyst 4096 Jul 18 10:10 scripts -rw-r--r-- 1 analyst analyst 25553 Feb 13 2017 SQL_Lab.pcapCompare the permissions of the malware directory with the mininet_services file.
Computer Science & Information Technology
Regarding protection domains, when an object from one domain calls code from another domain, the rule of ____ is employed.
A. uniqueness B. complement C. union D. intersection
Computer Science & Information Technology
Which of the following is an operation of the ADT list?
a) pop b) dequeue c) peek d) remove
Computer Science & Information Technology