FIGURE EX 8-1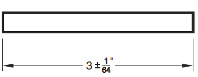 The commands in the accompanying figure are available on the ____ tab.
The commands in the accompanying figure are available on the ____ tab.
A. File
B. View
C. Page Layout
D. Data
Answer: D
Computer Science & Information Technology
You might also like to view...
Wireless authentication first requires the wireless device-not the user-to be authenticated before being connected to the WLAN.
Answer the following statement true (T) or false (F)
Computer Science & Information Technology
Discuss the considerations as you choose the BackColor of a window.
What will be an ideal response?
Computer Science & Information Technology
A ____ policy prevents a document or script loaded from one "origin" from accessing or modifying the properties of a document from a different "origin."
A. same-origin B. trust domain C. cross-certification D. cross-domain
Computer Science & Information Technology
By the time you are ready to create comps for a website project, you should have the content at your disposal.
Answer the following statement true (T) or false (F)
Computer Science & Information Technology