________ floods a computer with requests until it shuts down and refuses to answer any requests for information.
A. A Trojan horse
B. A polymorphic virus
C. A DDoS attack
D. Pretexting
Answer: C
You might also like to view...
When either a selection structure's true path or its false path contains another selection structure, the inner selection structure is referred to as a(n) ____ structure.
A. indented B. nested C. nested selection D. indented selection
Which of the following statements is false?
a. A method reference of the form objectName::instanceMethodName is a bound instance method reference. b. A method reference of the form ClassName::staticMethodName is a static method reference. c. Collectors method joining is a collector that creates a concatenated String representation of the stream’s elements, appending each element to the String separated from the previous element by the joining method’s argument. d. All of the above statements are true.
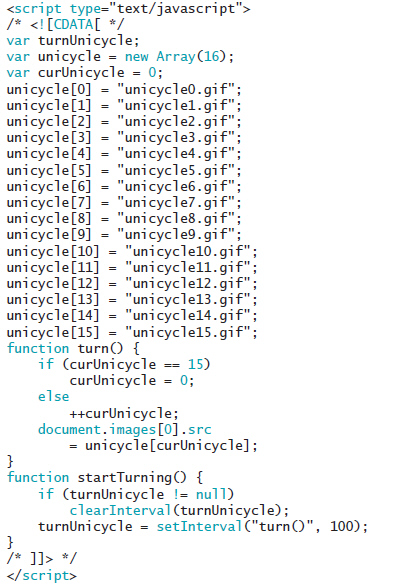 In the code seen in the accompanying figure, why does the startTurning() function check to see whether the value of turnUnicycle is null?
In the code seen in the accompanying figure, why does the startTurning() function check to see whether the value of turnUnicycle is null?
A. To make the animation smoother. B. To cache images. C. To prevent multiple button clicks starting the setting several intervals. D. To prevent errors if the images are not found.
____________________ is a measurement of the lightness or darkness in the color and is also measured as a percentage.
Fill in the blank(s) with the appropriate word(s).