Case EX 8-1Candace wants to create a chart sheet similar to the one shown above.Candace wants to move an embedded chart into a chart sheet. To do this, she would click the Chart Tools Design tab on the Ribbon. Then, in the ____ group, click the Move Chart button.
A. Location
B. Move
C. Chart Sheet
D. Chart
Answer: A
You might also like to view...
Worksheets can be protected for all of the following reasons EXCEPT:
A) data can be entered into only selected cells. B) formulas for automatically updated cells are protected. C) once protection is set ON, no further changes can be made. D) when saved as a template, all derived worksheets are protected.
Your company has invested an increasing amount in security due to the changing threat landscape. The company is trying to reduce costs, and the CFO has queried the security budget. At the same time, you as the security practitioner are actively requesting additional funding to support new initiatives. These initiatives will mitigate several security incidents that have occurred due to ineffective
controls. You assess the current controls framework and provide recommendations on whether preventative, detective, or corrective controls should be implemented. How should you explain which controls to implement? A. While corrective controls are more costly to implement, they are only needed for real attacks on high value assets. Put controls in place after a real attack has occurred. B. Detective controls are less costly to implement than preventative controls and should be encouraged wherever possible; corrective controls are used during an event or security incident; and preventative controls are hard to achieve in practice with current market offerings. C. Use preventative controls as this will prevent security incidents from occurring in the first place. Detective and corrective controls are redundant compensating controls and are not required if preventative controls are implemented. D. Use preventative controls before an event occurs; use detective controls during an event; and use corrective controls after an event has occurred. Use a combination of controls.
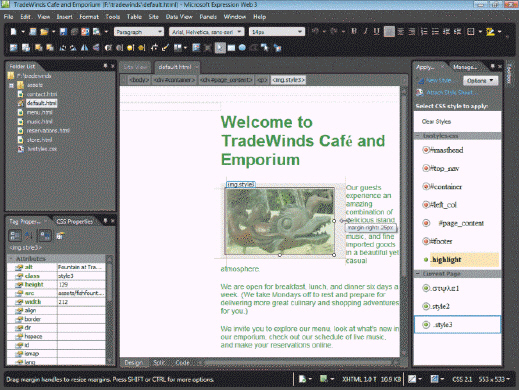 Referring to the figure above, after you make the necessary adjustments to the photo, Expression Web creates a class-based style rule and applies it to the ____ tag to control the alignment and margins of the image.
Referring to the figure above, after you make the necessary adjustments to the photo, Expression Web creates a class-based style rule and applies it to the ____ tag to control the alignment and margins of the image.
A.
B.
C.
Which protocol do Internet games employ to send information using ports reserved by the game?
A. FTP B. TCP/IP C. SMTP D. Telnet