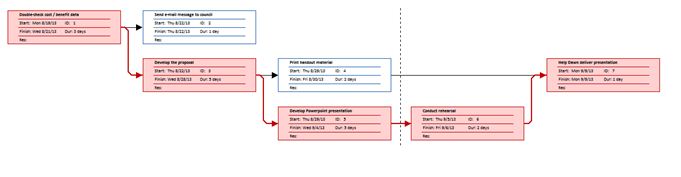
Create a PERT chart that shows the project. Use a format similar to Figure 3-18 on page 82. If project management software is available, use it to develop the chart.
What will be an ideal response?
Computer Science & Information Technology
You might also like to view...
Hardware-based security controls include _____.
A. password fields B. online forms C. system patterns D. biometric devices
Computer Science & Information Technology
A Dataset is a copy of the data that can be accessed by an application.
Answer the following statement true (T) or false (F)
Computer Science & Information Technology
Which of the following represents the Copy button?
A. ![]()
B. ![]()
C. ![]()
D. ![]()
Computer Science & Information Technology
Which ios formatting flag can you use with a stringstream object?
A. precision() B. setf(ios:: fixed) C. Both A & B D. none of the above
Computer Science & Information Technology