DoS attacks can cause harm by ____.
a. stopping a critical service
b. slowly degrading services over a period of time
c. Both stopping a critical service and slowly degrading services over a period of time
d. Neither stopping a critical service nor slowly degrading services over a period of time
a. stopping a critical service
b. slowly degrading services over a period of time
You might also like to view...
If memory is an issue rather than speed, and we have a sparse graph with a high number of vertices, it would probably be best to implement it with a(n):
A. linked list B. adjacency matrix C. adjacency list D. priority queue
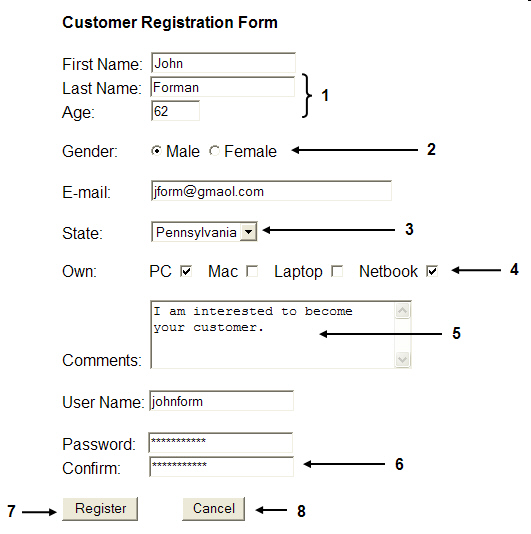 The ____ attribute for the item marked 7 in the accompanying figure is Register.
The ____ attribute for the item marked 7 in the accompanying figure is Register.
A. selection B. option C. value D. key
The UNIX I/O system is divided into the block I/O system and the interactive I/O system.
Answer the following statement true (T) or false (F)
At what frequency range do the 802.11b- and 802.11g-based wireless technologies operate?
A. 2.4 GHz B. 3.4 GHz C. 4.4 GHz D. 5.4 GHz